Photo via PCGAMER
Yesterday (14th May), Intel shared details on a new group of vulnerabilities called Microarchitectural Data Sampling (MDS). The vulnerability affects most of the Intel’s Chip out since 2008. The only exception being 8th and 9th generation Core Processor, as well as the 2nd generation XeonScalable Processors, which Intel said, carries hardware mitigations against the flaw.
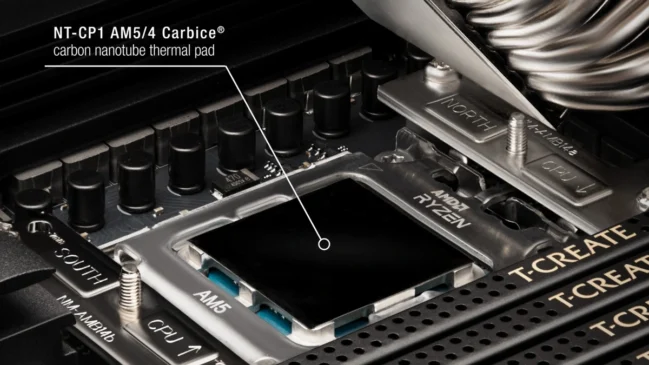
Currently, only Intel CPUs are affected by MDS, while others weren’t affected by the issue. (i.e. AMD, ARM, etc.)
MDS is similar to Spectre and allows speculative execution of side-channel attack that may allow malicious program to locally execute order and read data that program otherwise would not be able to see bypassing Intel’s inbuilt protections.
As for mitigation, Intel will be releasing microcode updates as part of regular Bios update with OEMs and updates to operating systems via vendors (i.e. Microsoft, Apple, etc.). Intel believes these mitigations when enabled would have minimal performance impacts for the majority of PC clients. But, Performance or resource utilization on some data center workloads may be affected and may vary accordingly.
The makeshift solution that Intel is pushing out will involve clearing of CPU buffers when switching between a trusted software too not trusted software (software not trusted by previous software). This extra step will add significant load on processing and most likely lead to performance loss.
Soon certain reports started claiming that Intel recommends Disabling Hyper-Threading in their processors to mitigate the issue fully, although these reports were later addressed by Intel where they said that “Intel does not recommend everyone to disable Hyper-Threading, but that some of its customers should consider the option depending on their security needs”
Recently, Intel’s HT technology had become less secure and slower and Intel themselves are moving away from HT on some of its best CPUs (such as i3,i5,i7) even when their competitor (AMD) is pushing similar technology on even low budget chips. AMDs implementation of HT is called SMT and according to them SMT is built on latest Microarchitectural advances and is more secure than Intel’s HT and doesn’t allow side channel speculative execution attacks, while also retaining significant performance advances.
It is yet to be seen how these mitigation are handled between OEMs and vendors, while some old motherboards and CPUs may not receive the Bios update and only receive software mitigation through OS.